But in 2015, the AVG mobile security team discovered a new strain of malware that may challenge this preconception. It’s a type of spyware known as Android/PowerOffHijack, which takes over the shutdown process to make your phone appear as though it’s powered off, even though it’s still working.

First seen in China, the spyware spread through Chinese app stores and infected thousands of devices with Android versions older than v.5 (Lollipop). Users must grant root permission to the malware in order for it to hijack the shutdown process.
After pressing the power button, the phone displays an authentic shutdown animation, and the phone appears as though it’s been powered down. But though the screen is black, the phone is actually still on.
While the phone is in this state, the Android/PowerOffHijack spyware can make outgoing calls, take pictures, and perform many other tasks without notifying you.
How does this happen?
Analysing the Android shutdown process
On Android devices, when the power button is pressed, the malware will invoke the interceptKeyBeforeQueueing function. interceptKeyBeforeQueueing will check if the power off button is pressed, and then proceed through the following process.
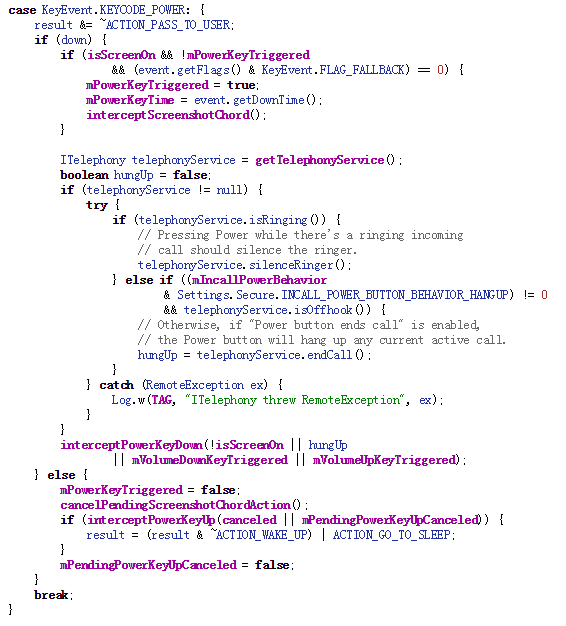 When the power button is released, interceptPowerKeyUp is invoked, triggering another runnable process.
When the power button is released, interceptPowerKeyUp is invoked, triggering another runnable process.
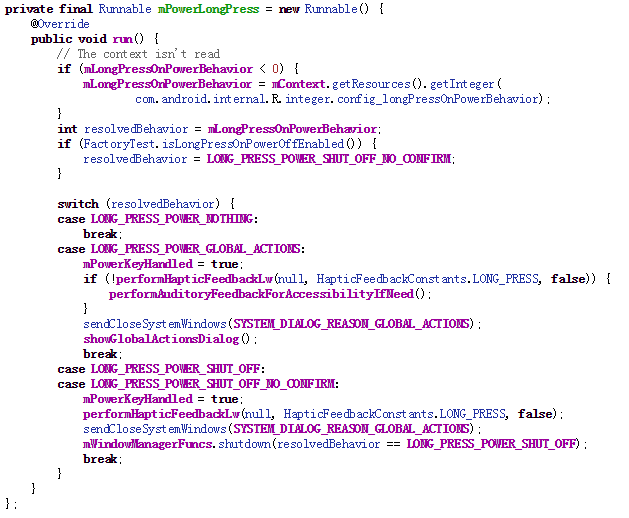 According to the above code snippet, the LONG_PRESS_POWER_GLOBAL_ACTIONS switch indicates that some actions will be taken after the power button is released. The showGlobalActionsDialog will open a dialog to allow you to set your phone to power off, go on mute, or activate airplane mode.
According to the above code snippet, the LONG_PRESS_POWER_GLOBAL_ACTIONS switch indicates that some actions will be taken after the power button is released. The showGlobalActionsDialog will open a dialog to allow you to set your phone to power off, go on mute, or activate airplane mode.
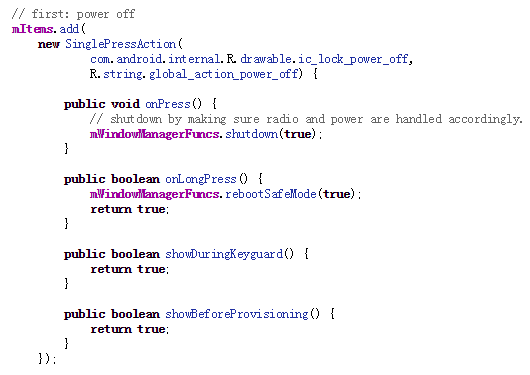 If you select the power off option, the malware calls up mWindowManagerFuncs.shutdown.
If you select the power off option, the malware calls up mWindowManagerFuncs.shutdown.
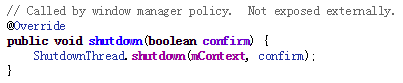
But mWindowManagerFuncs is an interface object, which will actually call the ShutDownThread shutdown function. ShutDownThread.shutdown is the actual start of the shutdown process. It will shut down radio service first and invoke the power manager service to turn the power off.
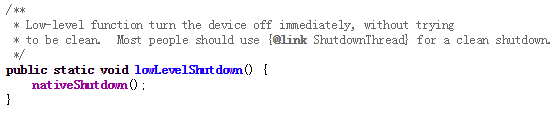
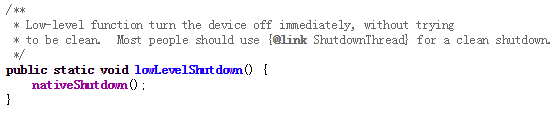
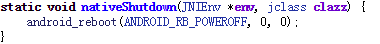
Finally, in the power manager service, a native function is called to turn the power off.
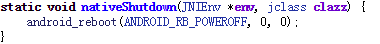 Since mWindowManagerFuncs.shutdown deactivates the phone’s radio services, any malware that aims to hijack the power-off process would need to interfere before this function activates. Let’s see how Android/PowerOffHijack gets this done.
Since mWindowManagerFuncs.shutdown deactivates the phone’s radio services, any malware that aims to hijack the power-off process would need to interfere before this function activates. Let’s see how Android/PowerOffHijack gets this done.
Analysing the malware
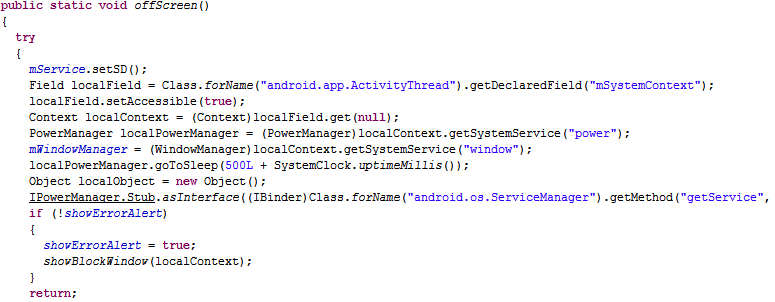
First, Android/PowerOffHijack applies for root permission. After getting it, the spyware will inject the system_server process and hook the mWindowManagerFuncs object.
At this point, when you press the power button, you’ll see a fake dialog instead of the authentic Android version. And if you select power off, you’ll get a fake shutdown animation, leaving the power on but the screen off.
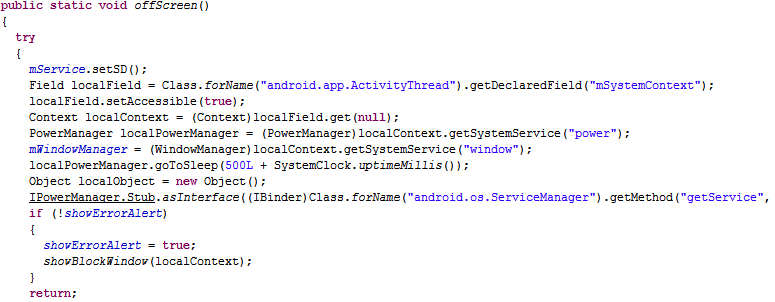
Finally, in order to make your mobile phone look like it’s really off, some system broadcast services also need to be hooked.
Let’s look at some examples:
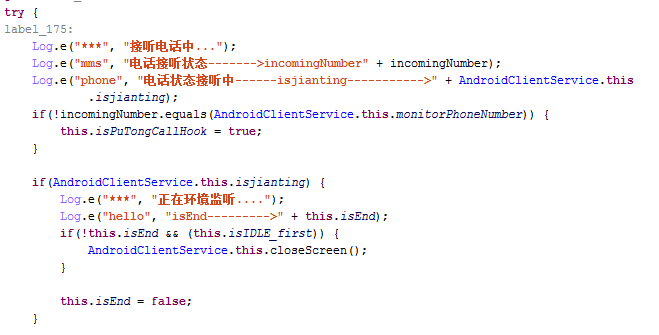
Recording a call
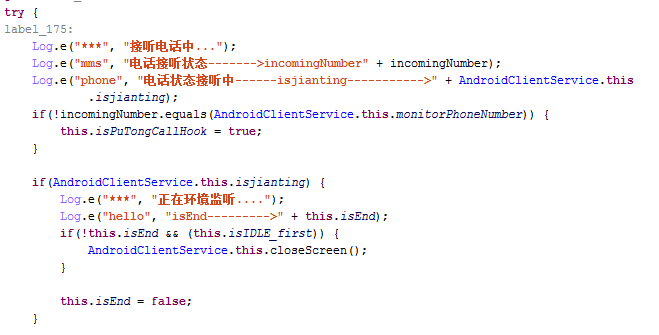
Transmitting private messages

Fight against spyware with AVG AntiVirus for Android
Even the sneakiest spyware like Android/PowerOffHijack is no match for AVG AntiVirus for Android. Our comprehensive mobile security tool will scan your device to detect and remove malware, and also keep you safe against future attacks. Protect your devices against spyware, viruses, and other malware, and keep your data safe from real-world thieves as well with the built-in Anti-Theft Phone Tracker.


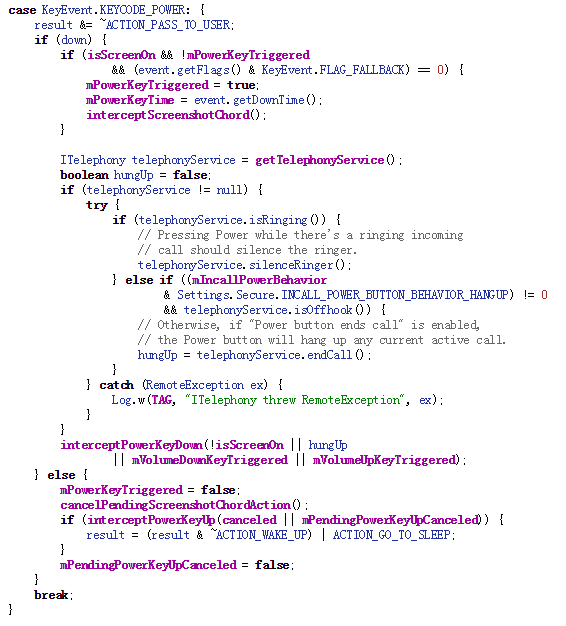 When the power button is released, interceptPowerKeyUp is invoked, triggering another runnable process.
When the power button is released, interceptPowerKeyUp is invoked, triggering another runnable process.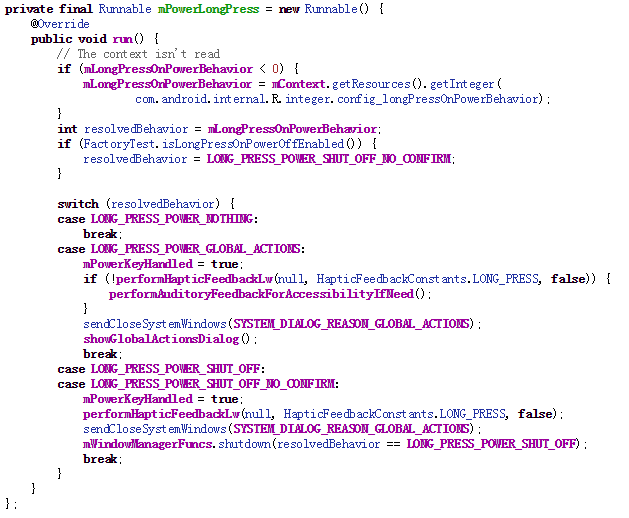 According to the above code snippet, the LONG_PRESS_POWER_GLOBAL_ACTIONS switch indicates that some actions will be taken after the power button is released. The showGlobalActionsDialog will open a dialog to allow you to set your phone to power off, go on mute, or activate airplane mode.
According to the above code snippet, the LONG_PRESS_POWER_GLOBAL_ACTIONS switch indicates that some actions will be taken after the power button is released. The showGlobalActionsDialog will open a dialog to allow you to set your phone to power off, go on mute, or activate airplane mode.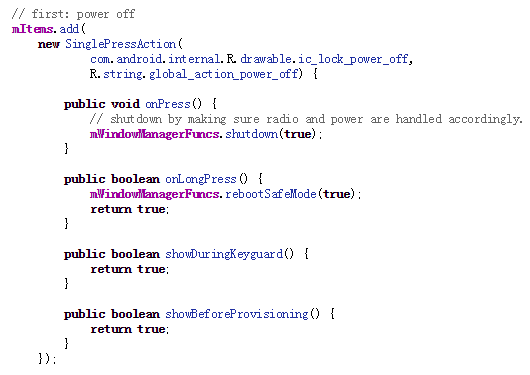 If you select the power off option, the malware calls up mWindowManagerFuncs.shutdown.
If you select the power off option, the malware calls up mWindowManagerFuncs.shutdown.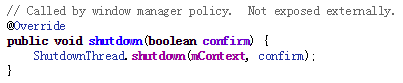
 Since mWindowManagerFuncs.shutdown deactivates the phone’s radio services, any malware that aims to hijack the power-off process would need to interfere before this function activates. Let’s see how Android/PowerOffHijack gets this done.
Since mWindowManagerFuncs.shutdown deactivates the phone’s radio services, any malware that aims to hijack the power-off process would need to interfere before this function activates. Let’s see how Android/PowerOffHijack gets this done.